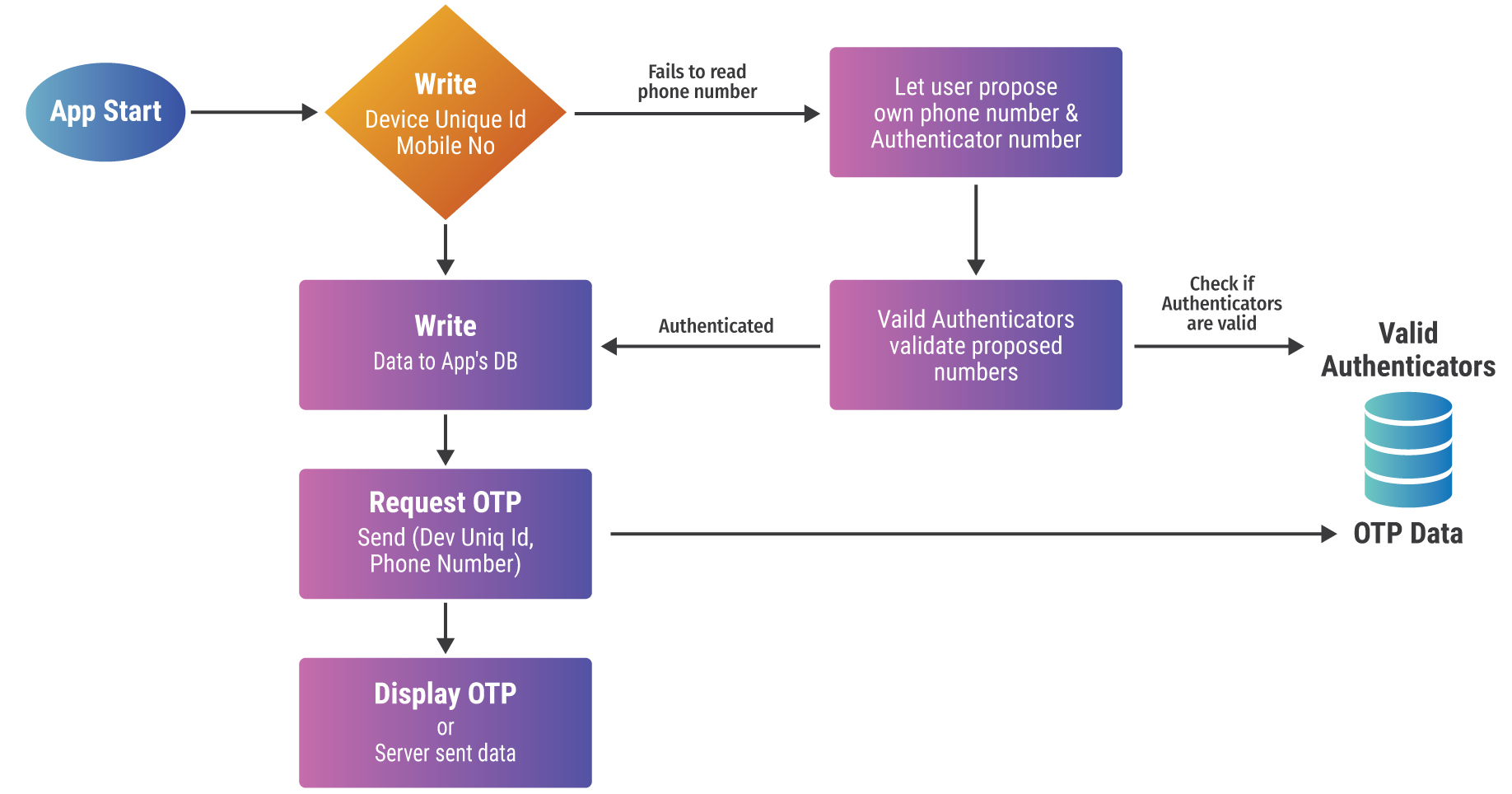
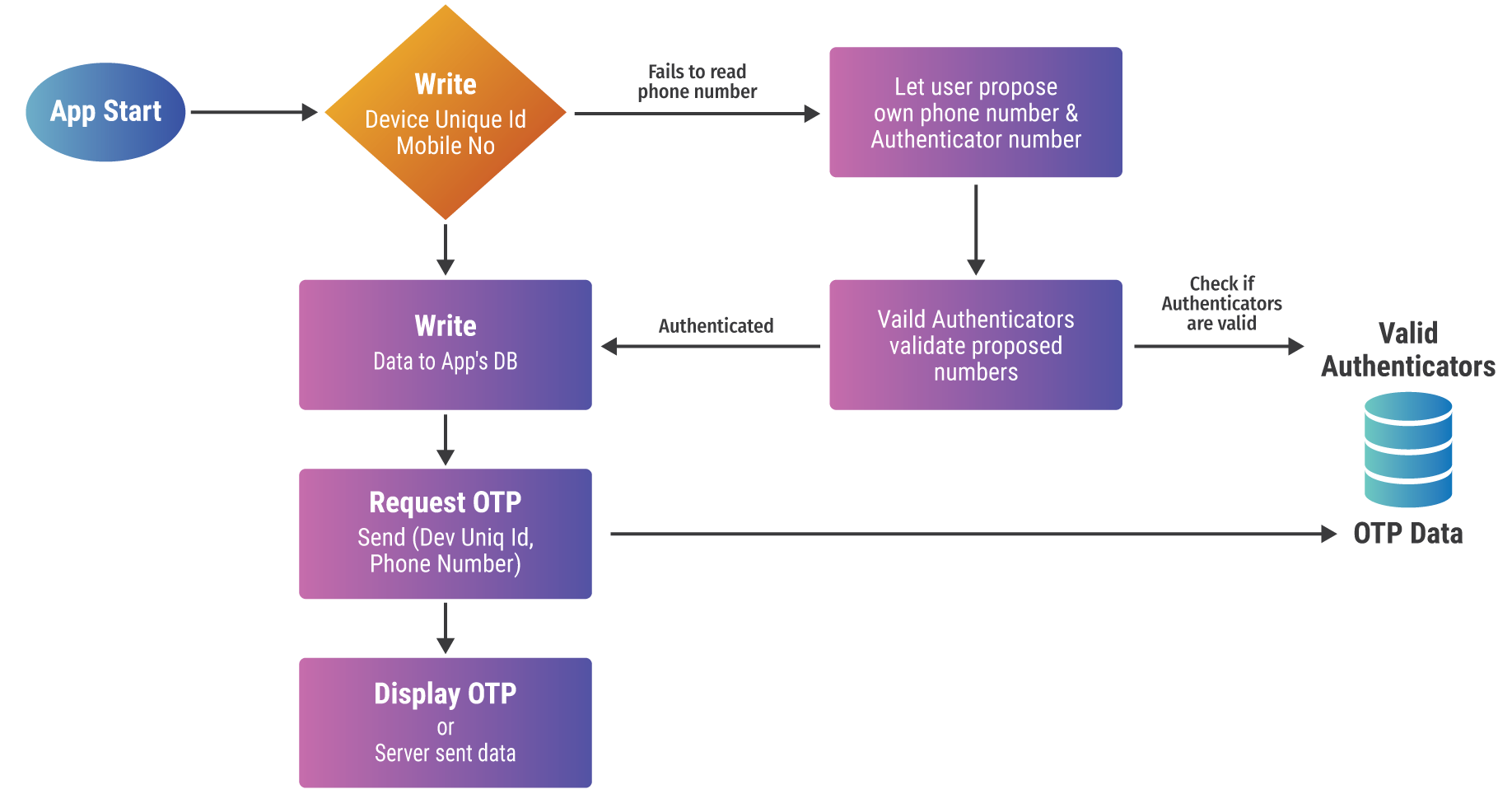
Step-by-Step Flow
The GetOTP system operates with minimum friction and maximum security. Here’s how it works:
Mobile Number Detection
When the app is first installed, it automatically attempts to detect the user’s mobile number (if permissioned). Alternatively, it can be securely provided via the host authenticator app and locked to the device to prevent spoofing.
OTP Generation (Host-Side)
The host system continues to generate OTPs based on its usual logic — time-based, random string, or user-triggered.
Device Recognition
The app identifies the user’s device using the Android ID and the associated mobile number. This replaces the need for login or SMS verification.
User Requests OTP
When the user opens the app, it makes a secure call to the backend to fetch the current OTP.,/p>
Server Validation
The backend checks whether the OTP is still valid, verifies the device ID against the expected mapping, and ensures no tampering has occurred.
OTP Display
Once validated, the OTP is displayed on- screen, never shared with the clipboard or other apps. The OTP disappears after a set duration or when used.
This flow ensures that users always receive their OTP on time — no SMS delays, no spoofing, and no access hurdles.
Benefits
- Bypasses SMS Weaknesses: No more waiting for SMS to arrive. No more fights with the mobile network operator. GetOTP delivers consistently over any internet connection.
- No Onboarding Required: Users don’t need to sign up, log in, or share personal information. Device recognition is fully silent and secure.
- Easy Integration: Organizations don’t need to overhaul their backend systems. GetOTP is compatible with existing OTP generation logic.
- Flat Cost Model: Unlike SMS gateways that charge per OTP, GetOTP runs on your server’s bandwidth — lakhs of OTPs with zero messaging cost.
- Stronger Privacy & Security: The app doesn’t read SMS, doesn’t store OTPs on-device, and doesn’t sync with cloud services. It’s phishing-resistant and data-minimal.
- Fewer Complaints, Higher Conversions: Apps and services that use GetOTP see fewer user complaints, fewer failed authentications, and smoother user journeys.
Fig 11.2 : Comparison between SMS Gateway, Firebase Push and GetOTP
The Future of GetOTP
The current version of GetOTP already solves one of the most persistent problems in digital ecosystems. But the team is committed to pushing its utility further with upcoming features that will make it even more flexible, secure, and auditable.
Roadmap
- QR-Based Device Linking: Allow OTP fetch via secure, time-limited QR sessions — great for desktop-web interactions.
- Tamper-Proof Audit Trails: OTP access logs hashed and chained to prevent tampering.
- Biometric OTP Protection: Allow OTPs to be visible only after fingerprint or face scan.
- Admin-Gated Visibility: Enable OTPs to be shown only during specific time windows or admin-controlled sessions.
- Shared Device Mode: Special profiles for Common Service Centres (CSCs), ATMs, or kiosk systems.
- Offline Cache (Optional): OTPs can be temporarily cached (encrypted) to enable offline retrieval in remote areas.
With these additions, GetOTP aims to become the digital backbone of secure, low-cost, and frictionless OTP delivery for both private and public digital infrastructure.
Conclusion
As digital trust becomes the currency of modern platforms, the humble OTP continues to play a starring role in user authentication. Yet, with SMS proving to be a fragile channel, we must ask — why rely on it?
GetOTP offers a bold, practical answer. It replaces outdated infrastructure with a simple, secure, and scalable model that just works — no matter where you are or how many OTPs you send.
In a world where users abandon carts, sessions expire, and networks drop signals — GetOTP delivers.