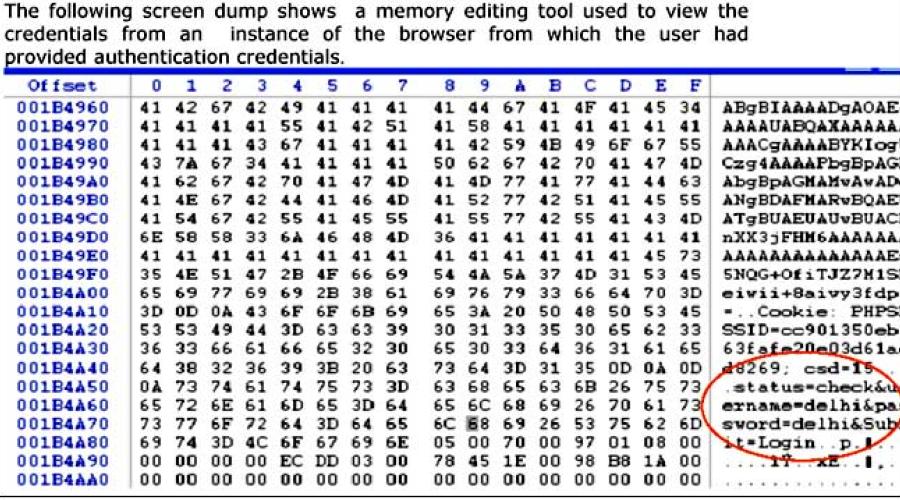
During the course of Penetration testing of Web Applications at Cyber Security Division, NIC, several security vulnerabilities are identified. One of these vulnerabilities includes the finding that the credentials traveling in clear text can be sniffed from the network. The credentials can also be detected with the help of memory editing tools on shared systems which are used to access the authentication web pages. Considering the common nature of these problems and their solutions, throwing light on the underlying concepts is a must read for those targeting the problem while developing secure code in an effective manner. The following section sheds light on the solution to the problem
Also read
NIC Strengthens Global Digital Cooperation through ICD Engagements…
The National Informatics Centre (NIC), through its International Cooperation Division (ICD…
Dyslexia‑Friendly UI/UX: Design Standards and Engineering Guidance for Inclusive Digital…
Technical and design standards for dyslexia-friendly UI/UX in digital government services…
Gov.in Secure Intranet: An AI-Powered Secure Digital Platform for Government
Gov.in Secure Intranet is a G2G digital platform developed by NIC under MeitY to support d…
MedLEaPR: Transforming India’s Medico-Legal Ecosystem
MedLEaPR is a national digital platform that streamlines medico-legal processes by securel…
NIC’s ServicePlus and UDISE+ Platforms Recognised at Aadhaar Samvaad…
Two flagship digital governance platforms developed by NIC ServicePlus and UDISE+ (Unified…
"Meri Panchayat” App Wins WSIS Prizes 2025 Champion Award
The “Meri Panchayat” mobile app, developed by the Ministry of Panchayati Raj and NIC, has…
United States Eyes Synthetic Data to Unlock Insights While Protecting…
As governments ook for new ways to use data without compromising citizen privacy, syntheti…
India and Mauritius Discuss Strengthening Digital Cooperation
Dr. Avinash Ramtohul, Hon’ble Minister of IT, Communications and Innovation of Mauritius,…
10 Indian AI Startups Selected for Global Accelerator in Paris
In a major boost to India’s global AI footprint, the IndiaAI Mission under the Ministry of…
India Highlights Inclusive Approach to AI Governance at UN…
At the launch of the Global Dialogue on Artificial Intelligence (AI) Governance at the Uni…