Case Study: DST Infrastructure Audit
In 2024, under the direction of MeitY, NIC initiated a large-scale cyber security infrastructure audit across several ministries and government departments at Central, State and District levels. Centre for Development of Advanced Computing (CDAC) had been entrusted to conduct Cyber Security Audit of Department of Science and Technology (DST) network in Technology Bhawan, The audit aimed to assess the overall cybersecurity posture of DST’s IT ecosystem—beyond just application-level vulnerabilities.
Scope of Audit
- Asset Identification and Discovery
- Network Architecture Review
- Endpoint Security and Configuration Review
- Internal and External VAPT (Vulnerability As sessment & Penetration Testing)
- System and Device Log Review
- Review of Cybersecurity Policies and Standard Operating Procedures (SOPs)
- Network Traffic Analysis
- Review of Network and Security Device Logs
- Risk Management Assessment
- Adherence to Best Practices and Auditor Recommendations
During the audit, teams from CDAC and NIC Cyber Security conducted a pre-audit assessment to understand the existing IT infrastructure as per Meity issued guidelines and, while the NIC team at DST shared details such as asset lists, network diagrams, configurations, security measures, whitelisted applications, logs, and incident history.
CDAC team collected and reviewed existing asset list, architecture diagram, and device configurations. Interacted with concern IT Team to understand current network infrastructure, network connectivity, followed practices, procedures, and configurations. The audit was conducted based on this information and further validated through onsite visits and system reviews.
CDAC submitted its audit report in April’25, highlighting vulnerabilities categorized as critical, high, medium, and low, which DST is expected to address. This was the initial step towards strengthening cyber security and will require follow-up after compliance actions are taken.
Findings
The exercise achieved most defined objectives and, for the first time, resulted in complete documentation of DST network, identifying key security gaps. This serves as a foundation for comprehensive gap analysis and implementation of the Cyber Crisis Management Plan.
The result? A clear, actionable roadmap to:
- Well documented assets and network details
- Streamline security processes
- Align with MeitY and CERT-In guidelines
- Support crisis management planning
Though the IT Infrastructure Audit is done, this audit cannot be considered as Information Security Audit as it has not covered other IT applications and portals used for implementation of its schemes and projects.
Mixed Response Across Departments
Some departments acted on the audit findings; others treated it as a mere formality. With out mandatory certification, follow-through was weak—especially under the assumption that government cloud hosting made formal certification unnecessary. The audit revealed a hard truth: infrastructure vulnerabilities are real, often undocumented, and remain unaddressed without systematic certification.
The Limitations of Application
Application security audits have long been a standard requirement for government portals and e-governance platforms to be hosted in National Data Centers. These audits typically review code vulnerabilities, test for common cyber threats as per OWAPS guidelines and provide a certificate that clears the application for deployment—often seen as the final green signal.
However, these audits are not sufficient to ensure real-world security, compliance, or longterm sustainability. Here’s why.
Common Gaps Observed
Despite years of mandated application security audits across ministries, several critical vulnerabilities and policy violations continue to go unchecked. These gaps highlight the limitations of conventional audits and the urgent need for structured certification frameworks like ISO 27001.
Limited Scope of Application Security Audit
Most application audits focus on code-level issues as per OWAPS guidelines —like SQL injection, XSS vulnerabilities, or insecure APIs—but rarely evaluate the application:
- Whether it follows government-approved security guidelines (like NISPG or eSAFE)
- Does meet data privacy laws such as the Digital Personal Data Protection (DPDP) Act, 2023
- If the system is designed for required performance and availability
- Do the system follow standard Change Management Policy?
- If disclaimers or user consent mechanisms exist before collecting personal data
- Whether change management or SOPs are documented and followed
- Whether the hosting system is hardened
- Any performance monitoring or reporting mechanism implemented
Insecure Authentication, Weak Identity and Access Management
Many applications continue to operate with:
- Poor Identity and password management
- Basic username-password logins (often without CAPTCHA),
- No multi-factor authentication (MFA),
- Default admin credentials or shared logins.
- Non enforcement of periodical password change.
Poor Design and Broken Workflows
Even when code is audited, functional flaws go unnoticed, leading to poor service delivery. For instance:
- Auto-logout mechanisms don’t work
- Role-based approvals are bypassed
- Logging mechanisms are incomplete.
- No standard support and redressal mechanism.
Non-Compliance with Accessibility Laws
Despite completing STQC certification, many portals:
- Do not meet WCAG 2.1 guidelines,
- Do not comply to DBIM guidelines
- Violating of Web Accessibility Guidelines had forced the Supreme Court ruling to implement WCAG 2.1 on priority. Violation may lead to monthly penalty.
Absence of Confidentiality Safeguards
- Non maintenance of Non-Disclosure by implementing agencies and outsourced employees.
- No documentation exists for human resource onboarding, offboarding, or data access boundaries.
Lack of User Consent and Data Sharing Disclaimers
Applications routinely collect sensitive user data but:
- Do not display Terms of Use or data-sharing consent notices
- Do not have policies for cross-system data exchange, putting departments at risk under the DPDP Act
Poor Readiness for Legal Compliance
More than 80% of audited applications are not equipped to demonstrate:
- Data retention and deletion policies,
- Log monitoring or breach detection systems,
- Compliance with the DPDP Act or IT Act 2000.
ISO 27001: What It Covers
In a digital ecosystem where data is the lifeblood of governance, security must extend beyond code-level audits and isolated technical fixes—it demands an integrated, holistic approach. True resilience demands a structured, organization-wide commitment to protecting information at every stage of its lifecycle. That’s where ISO/IEC 27001 steps in—not merely as a standard, but as a strategic framework for managing information security in a measurable, repeatable, and certifiable way.
Globally recognized and widely adopted across public and private sectors, ISO 27001 offers a blueprint for establishing a comprehensive Information Security Management System (ISMS). Unlike routine audits that often provide a narrow technical assessment, ISO 27001 looks at the entire organization—its people, policies, infrastructure, and technology—to ensure end-to-end accountability and risk management.
Domain | Clauses | Controls | Area |
|---|
Organizational | 5 | 37 | Policies, Role &Responsibilities, Risk & Asset management, Access control and identity management, Supplier relationship security, Incident response, Business continuity, Compliance with legal and regulatory requirements |
People | 6 | 8 | Pertaining to HR screening & qualifications before employment, T&C of Employment, ISMS Awareness, Training, Disciplinary Process, Responsibilities After Termination or Change of Employment, Confi dentiality or Non-Disclosure, Remote Working, Information Security Event Reporting |
Physical | 7 | 14 | Physical security perimeters like entry/ exit controls, physical security of the location, security monitoring, security of assets on-off premise, cabling security, equipment maintenance, secure disposal or reuse etc |
Technological | 8 | 34 | Access Control, Securing sensitive data, both in transit and at rest, Endpoint Protection, Logging and Monitoring, Backup and Recovery, Secure Development, Configuration Management, Data Deletion and Masking, Web Filtering and Secure Coding etc |
Fig 11.1 : ISO27001 : 2022 Domains and Controls
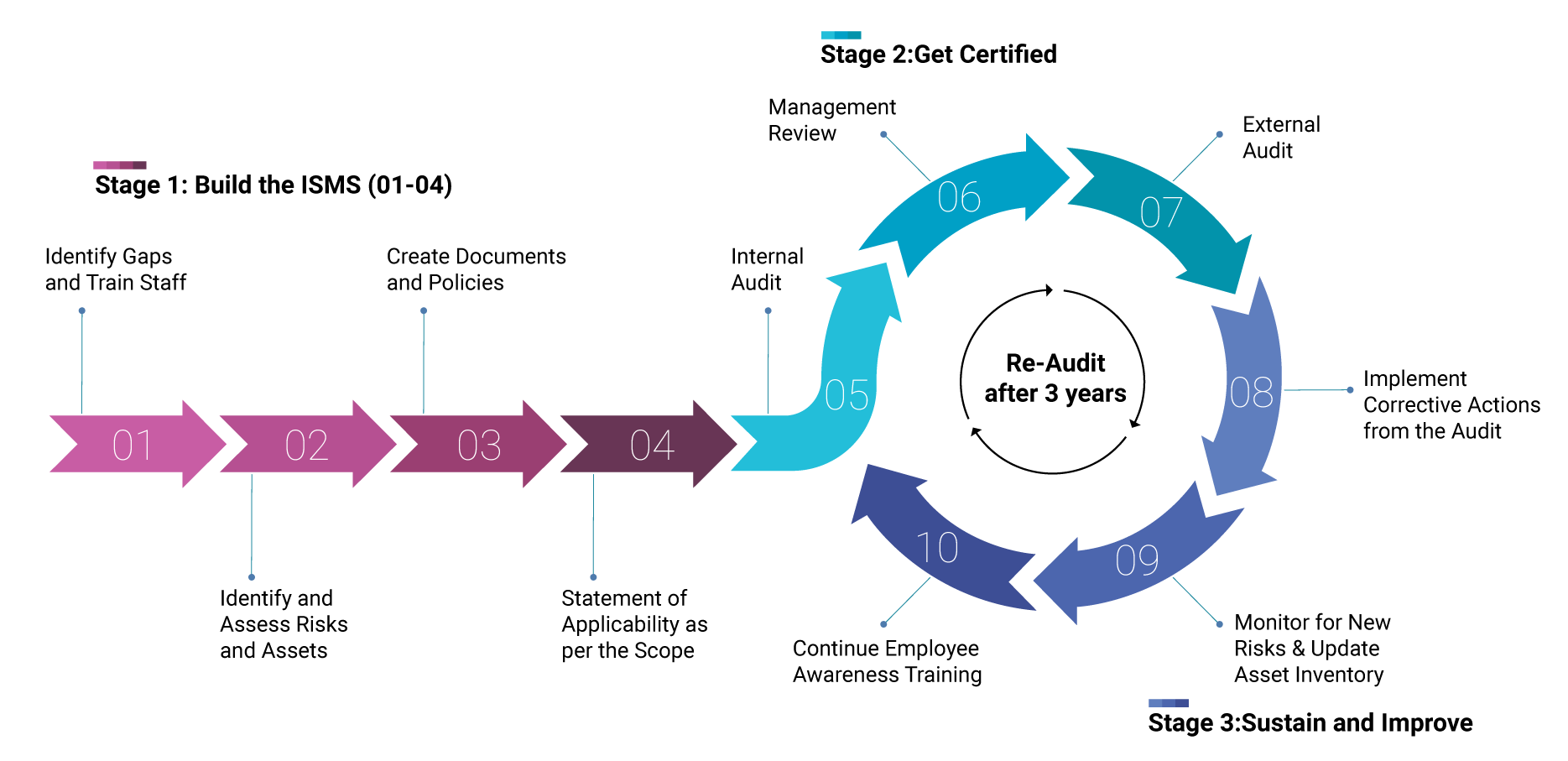
The ISO 27001 Certification Lifecycle
ISO 27001 certification is not a single event but a continuous lifecycle of building, validating, and improving an organization’s Information Security Management System (ISMS). It integrates internal discipline with third-party oversight and evolves as your organization grows, changes, and faces new risks.
The Four Pillars of ISO 27001
The 2022 revision of ISO/IEC 27001 organizes 10 clauses, with 93 security controls into four well-defined domains, each covering a critical area of information security. This structured approach ensures that all dimensions of an organization—people, processes, infrastructure, and technology—are systematically secured. Clause 1 to 3 pertaining to Scope and References, Clause 4 Context of organization. See fig. 11.1 for breakdown of the domains and their focus areas:
Clause 9 is related to Performance evaluation and Clause 10 for improvement.
The lifecycle can be broken down into three key stages: